Overview
A part of the standard WordPress package, Pingbacks allow remote blogs to notify your site when they have linked to your content. Unfortunately, hackers have found a way to exploit this in order to cause a Distributed Denial of Service (DDOS) attack against other websites and servers.
Unless you really understand what a pingback is, Conetix highly recommends that you disable pingbacks. This article guides you through the methods available to disable pingbacks.
Instructions
Apache based block
- To prevent access to the xmlrpc.php file, the easiest way is to edit your .htaccess. You can do this via the Plesk File Manager or edit locally and FTP the file back to the server. Add the following:
# XMLRPC Pingback DDOS Prevention
<Files xmlrpc.php> Order Deny,Allow Deny from all </Files>- This will block all access to the XML-RPC for WordPress as soon as the file is saved.
WordPress Toolkit
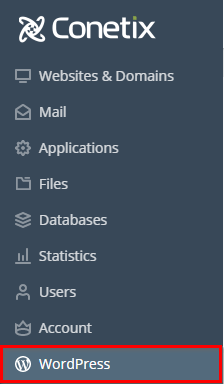
- Access your Plesk hosting with Conetix, for Shared Clients and VPS Clients
- In Plesk click WordPress on the left-hand side:
- In the WordPress Toolkit if your domain is collapsed like you want to click on the domain name or the arrow to expand it:

- Now under Status click Fix vulnerabilities:

- Then, Security Measures:

- In Security Measures, you want to tick the box for Block access to xmlrpc.php and Turn off pingbacks then up the top click Secure:

The order of the settings may change. - Once saved you have secured your site.
Further Reading
- Sucuri Blog: https://blog.sucuri.net/2014/03/more-than-162000-wordpress-sites-used-for-distributed-denial-of-service-attack.html
- Ars Technica: https://arstechnica.com/security/2014/03/more-than-162000-legit-wordpress-sites-abused-in-powerful-ddos-attack/
- Akamai Blog: https://blogs.akamai.com/2014/03/anatomy-of-wordpress-xml-rpc-pingback-attacks.html
